When working with multiple AWS accounts, it can be a pain to keep signing out and signing back in. I work with a number of accounts, my own, customer accts, burner accts, etc. It was a pain to keep logging in and out of the AWS Console. Thankfully the AWS Console has a "Role Switcher" that lets you quickly switch between accounts built-in. It does this by assuming a role from another account. Here's how to set that up...
Assuming you have a primary and new AWS accounts
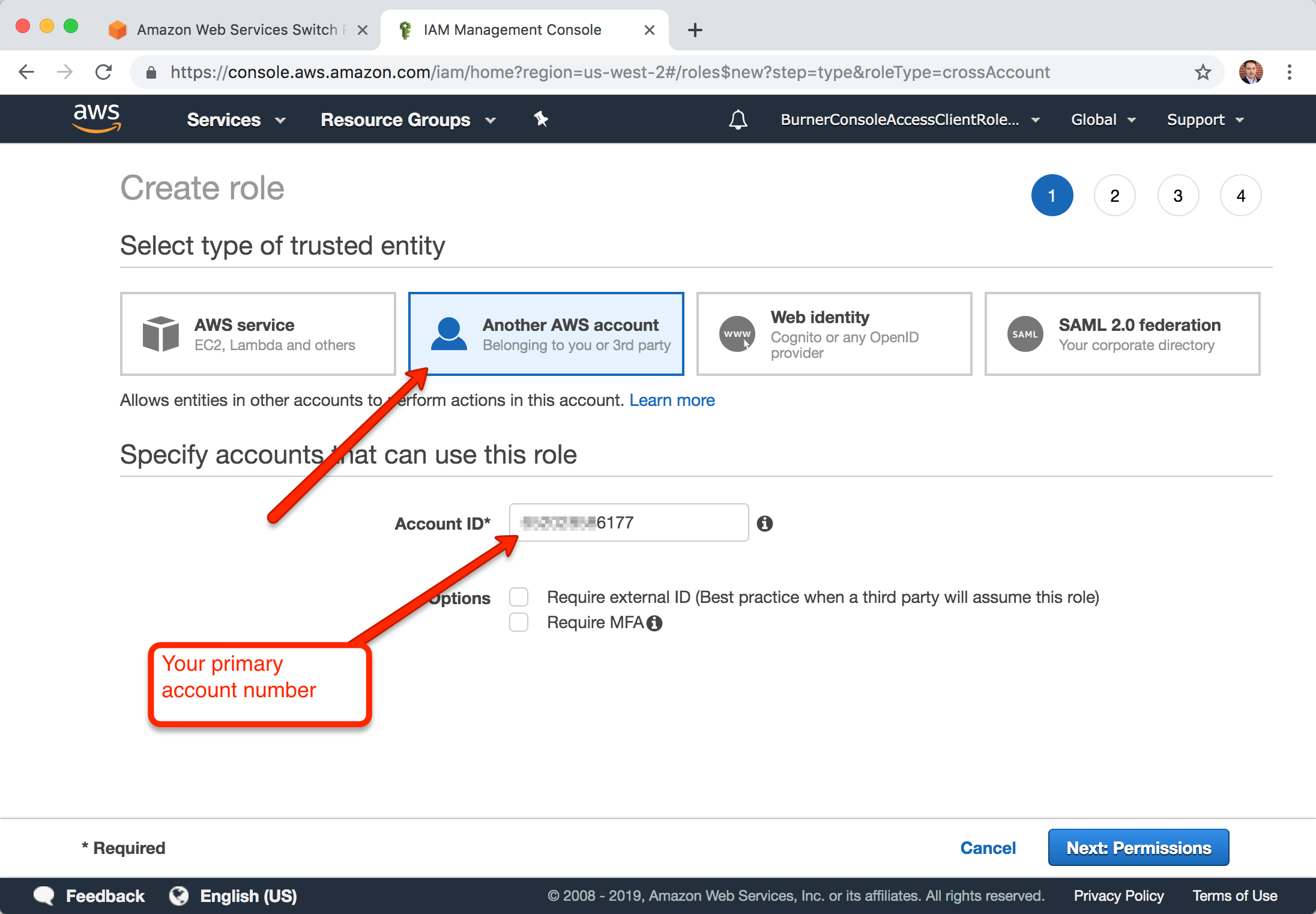
- From the new AWS account, add an IAM Role and instead of the tusted entity being "AWS Service", select "Another AWS account"
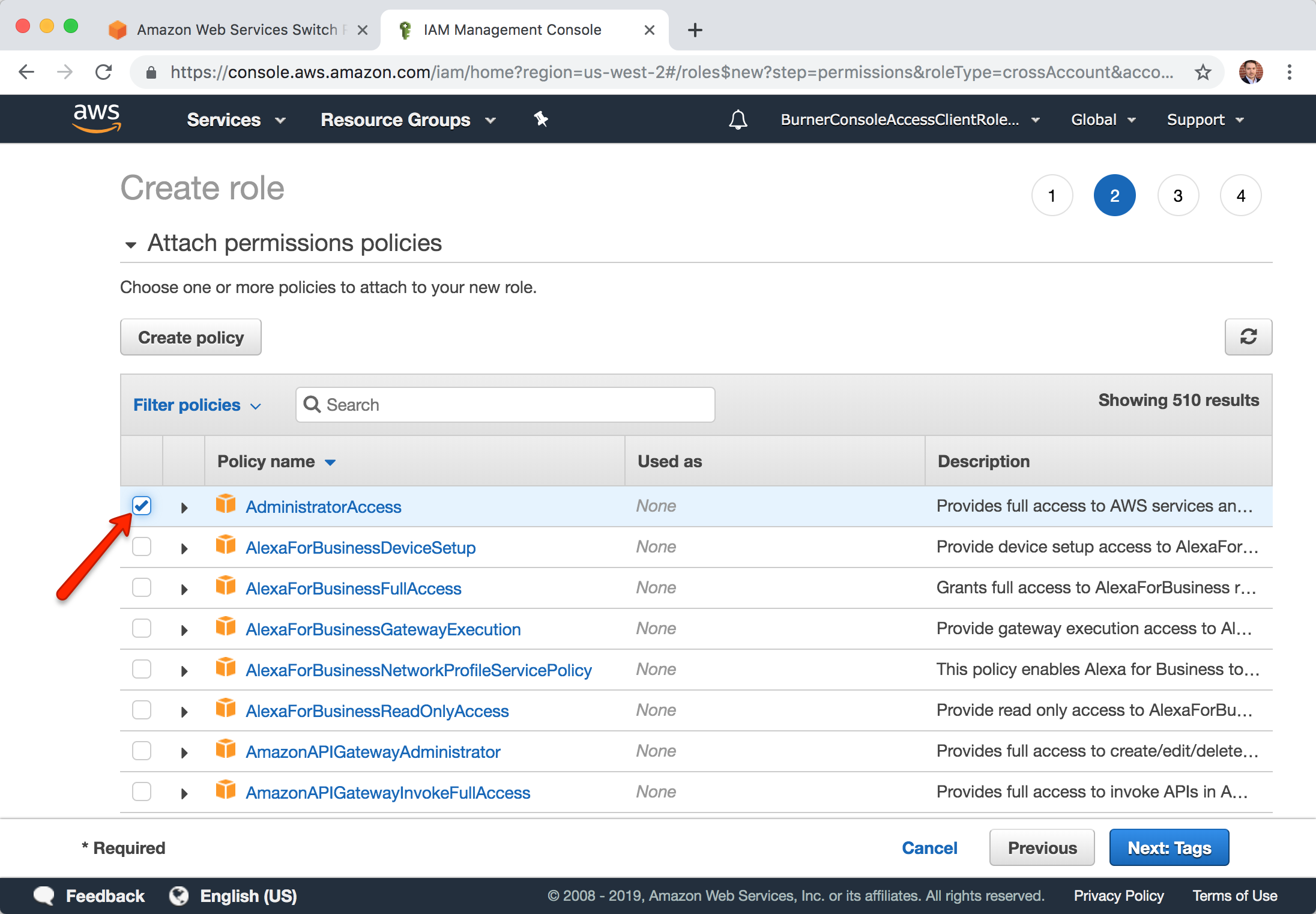
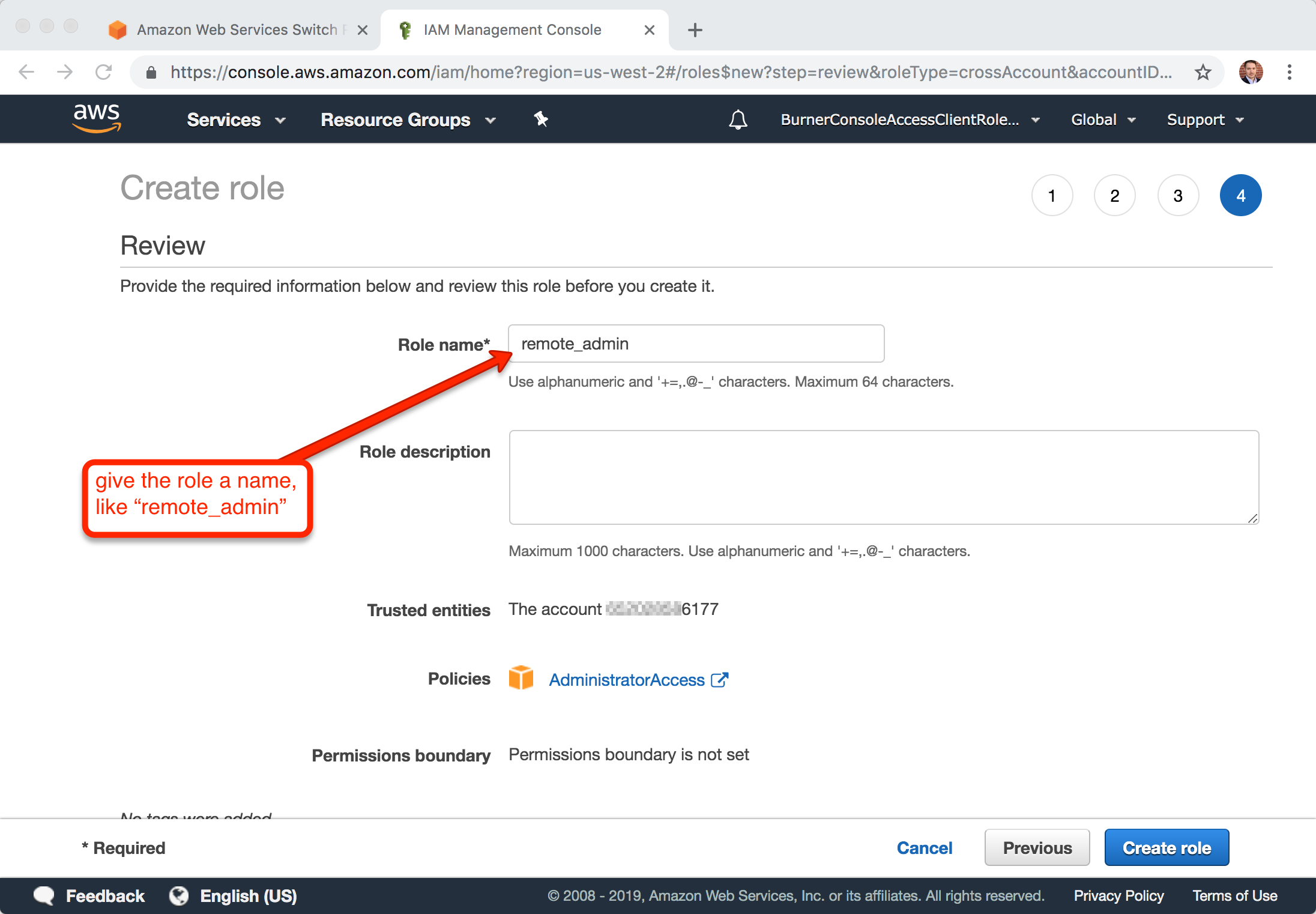
- Give it the account number of your primary account, choose your policy (like "AdministrativeAccess"), and give it a name.
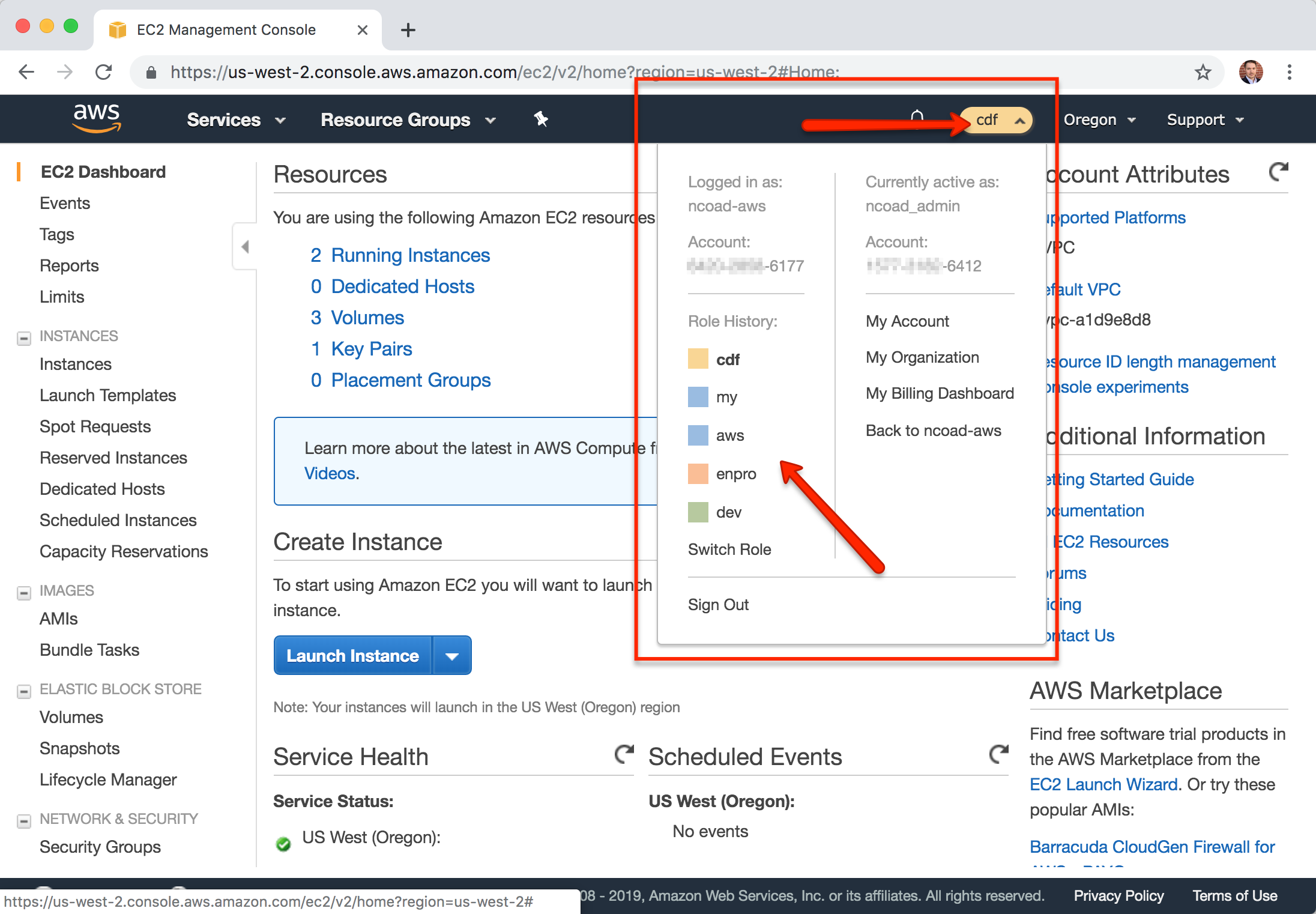
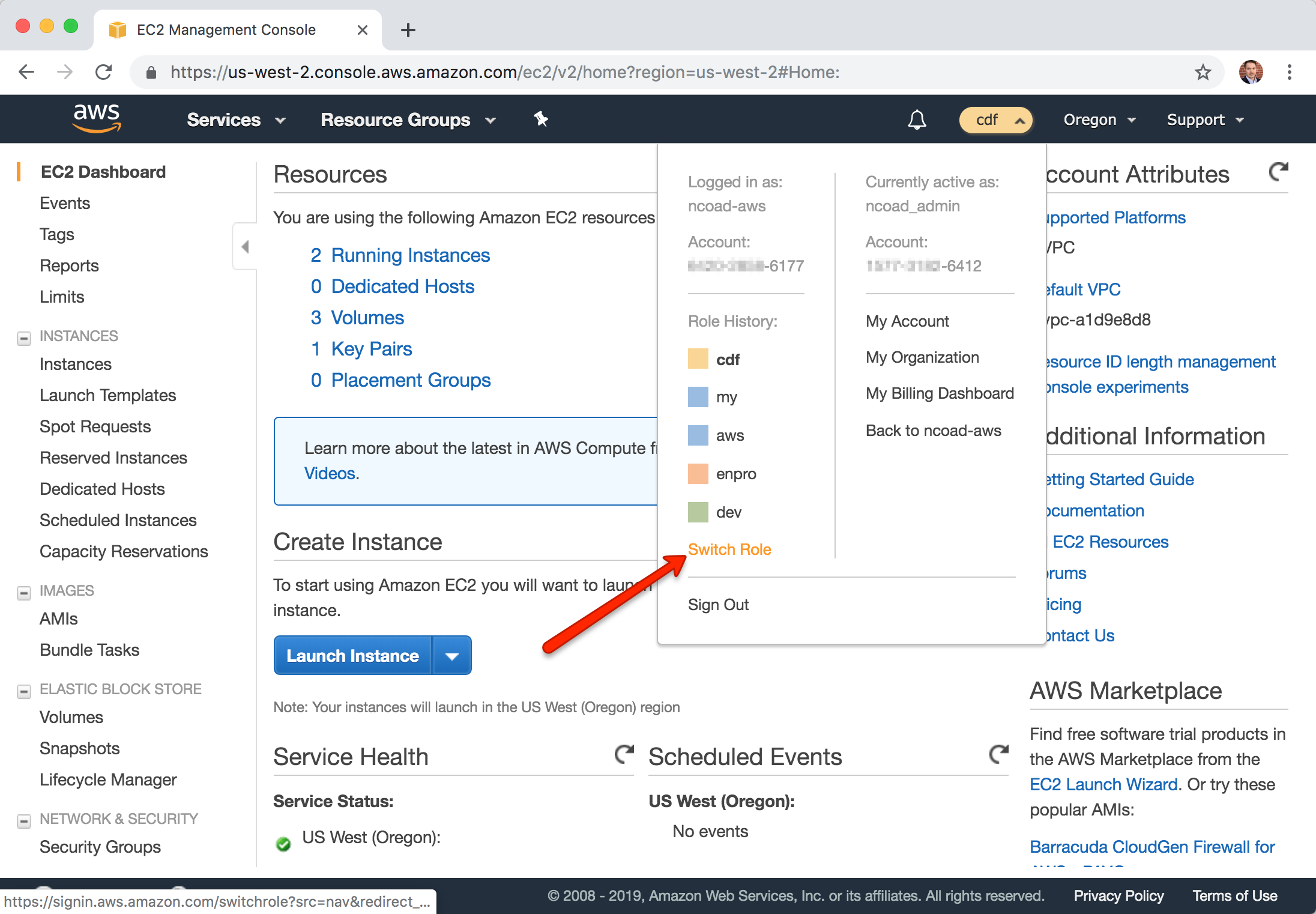
- From your primary account, select the login name in the top right of the screen and choose "Switch Role" from the menu.
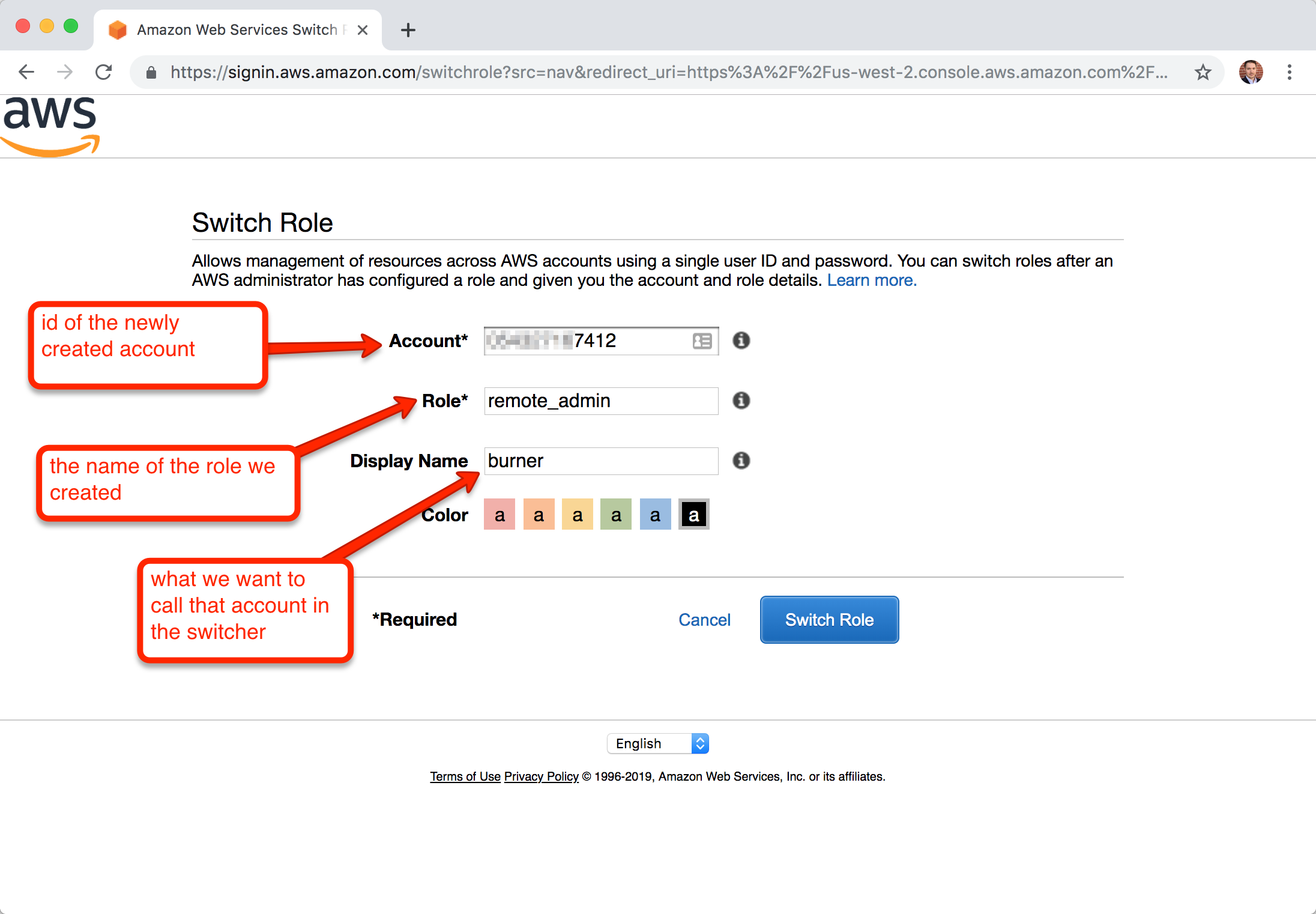
- Enter the new AWS account number, name of the IAM Role you created, a nickname and color.
Done.
For this, I'm going to say I have a primary account that I like to sign into AWS with. And I have a new account I'm calling burner that will be one of my many additional accounts I want in the switcher.
- Create a new AWS account
- From that account, add a new IAM Role. Choose "Another AWS Account" and enter the account # of the primary account.
- On "Attach permissions policies" page, choose a policy, like "AdministratorAccess"
- On "Review" page, give it a name, like "remote_admin"
- Sign out of the new account
- Sign into your primary account
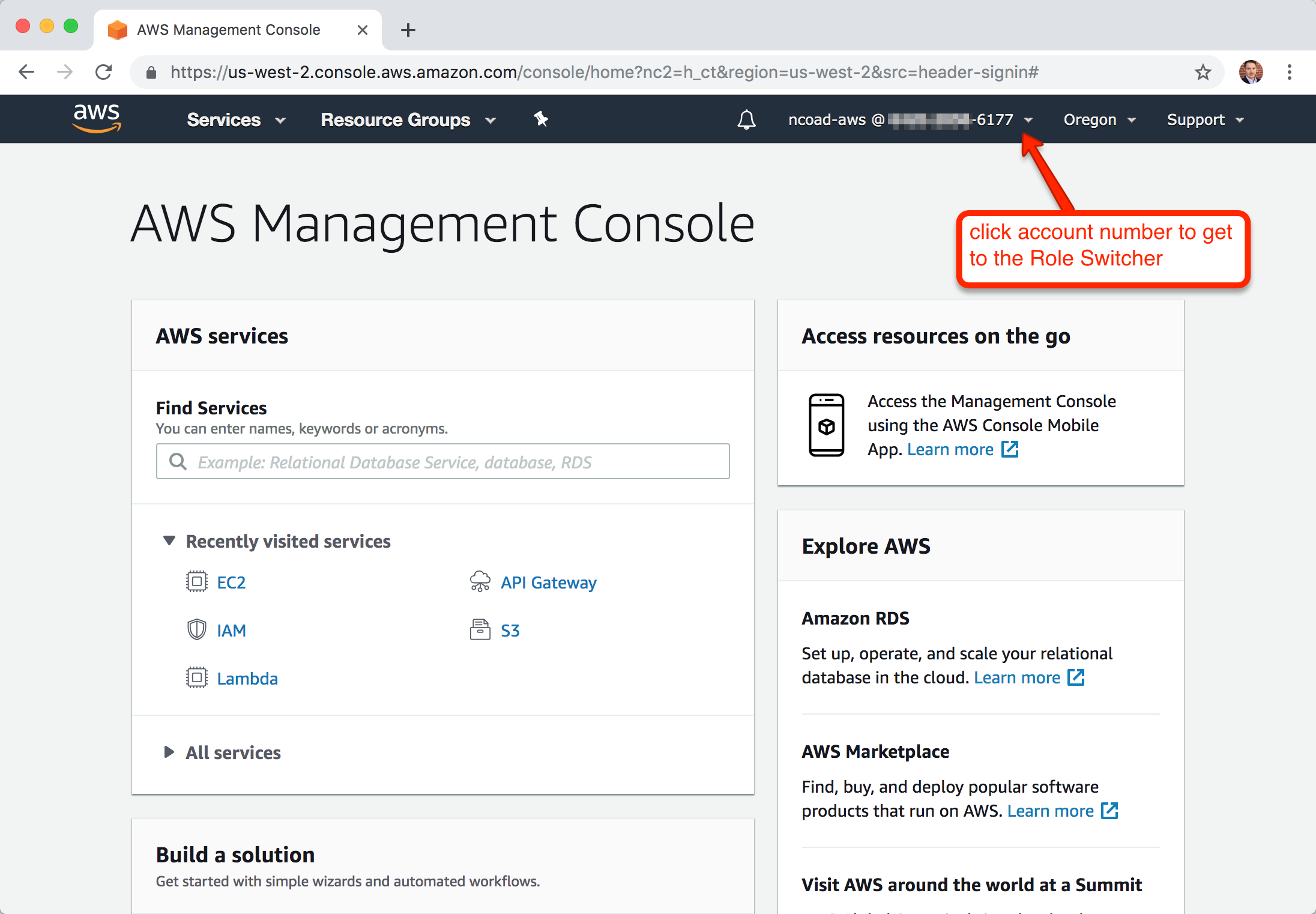
- Click on your account number on the top right of the console
- Choose "Switch Role"
- Enter: (a) the account ID for the new account, (b) the role you created (like "remote_admin"), and a (c) nickname and color you want to use in the switcher
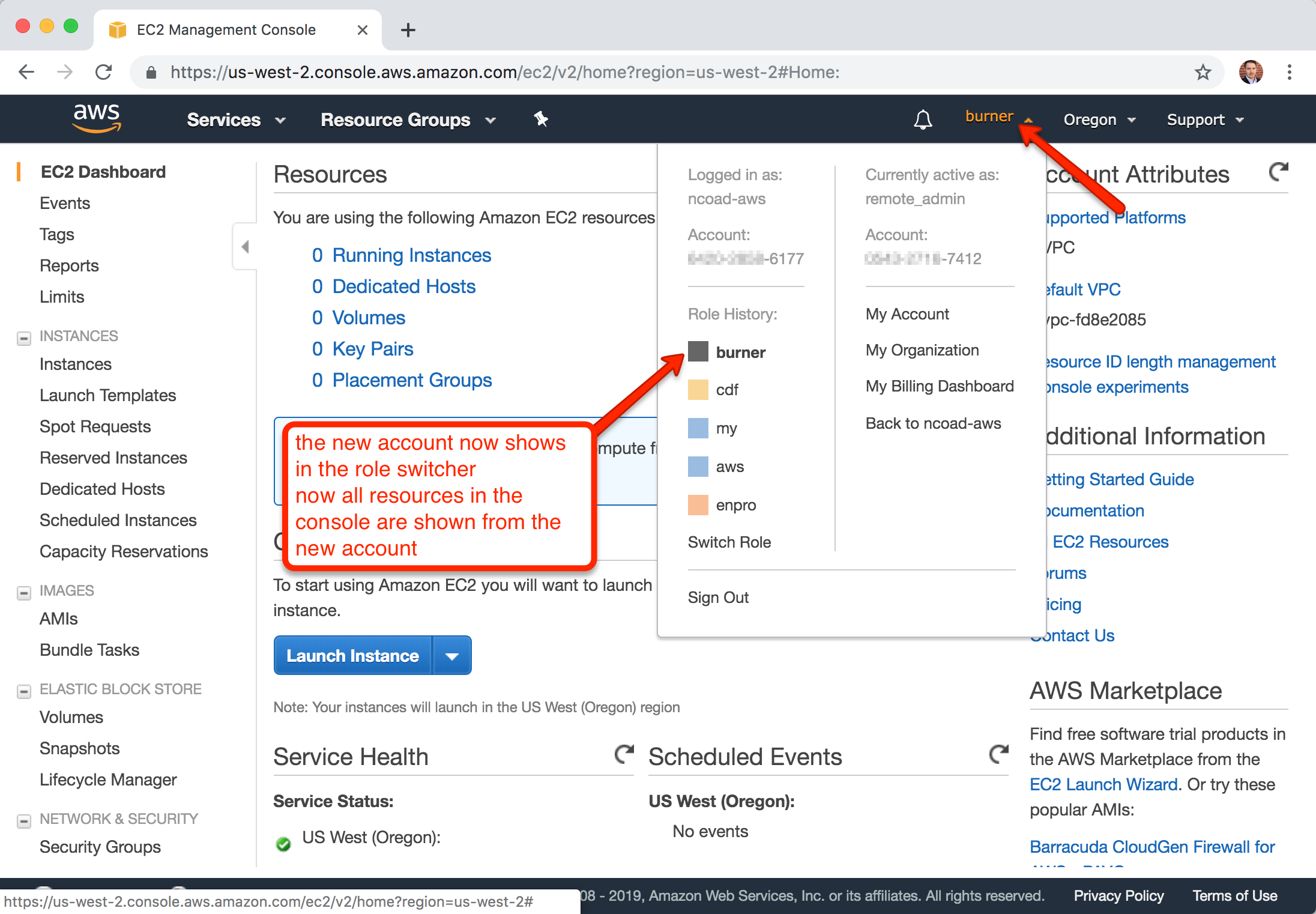
- Done! Now the account is in the Role Switcher drop down, and if you choose it everything you do in the console will be from that new account.
This also works with the aws command line interface tool.
It greatly simplifies the ~/.aws/credentials and ~/.aws/config files.
My ~/.aws/credentials file only has one 'access_key' and 'secret' entry to support over 20 accounts.
Example ~/.aws/credentials file with access_key and secret for only the master account:
[default]
aws_access_key_id = APIZJX29IUENNEB4XXXX
aws_secret_access_key = 8/eGdP9dwRkndy7liEPAzeLgSeBu/Kr7INg1xxxxEdit your ~/.aws/config file to add the new target account that has the new role:
[profile prod]
role_arn = arn:aws:iam::xxxxxxxxx7412:role/remote_admin
source_profile = defaultChange: xxxxxxxxx7412 to the target account number and remote_admin to the role name.
The new profile name we're going to use in this example is prod
Now you can use:
aws --profile prod sts get-caller-identityIf you want someone else to also have access, like a collegue to a shared dev account, you can go to the new role in the new account, "remote_admin" in this case, and edit the "Trust Relationship" to add their account to the same role.
There are situations that using an actual user is required or helps, such as:
- Creating S3 presigned URLs (
aws s3 presign) when assuming a role creates a much longer URL than as a user - You need a user for AWS CodeCommit git credentials
- Other related posts: Manage Multiple AWS Accounts with Role Switching